Trezor Login – Secure Access to Your Trezor Wallet
Managing cryptocurrency safely requires a trusted and secure login process. Trezor Login allows users to access and manage their digital assets through their Trezor hardware wallet while keeping private keys protected offline. Unlike traditional online wallets, Trezor uses hardware-based authentication to ensure that sensitive data never leaves the device.
With Trezor Login, users can connect their Trezor wallet to the official interface and safely send, receive, and monitor cryptocurrency holdings. The login process is designed to protect users from phishing attacks and unauthorized access while maintaining full control of their private keys.
What is Trezor Login?
Trezor Login refers to the secure authentication process used to access a Trezor hardware wallet through the official wallet interface. Instead of using a standard username and password system, the login process relies on the physical Trezor device for verification.
Key aspects of Trezor Login include:
- Hardware-based authentication
- PIN verification on the device
- Offline private key storage
- Secure access through Trezor Suite
- Protection against phishing attempts
This approach ensures that only the device owner can authorize transactions or access wallet features.
Trezor Hardware Wallet Devices



Trezor hardware wallets are designed to provide maximum security for cryptocurrency storage and transactions.
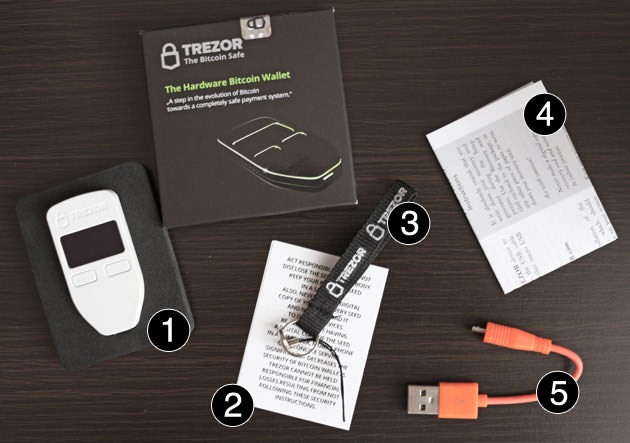
Trezor Model One
The Trezor Model One is the original hardware wallet introduced to offer a simple yet secure way to protect cryptocurrency. It supports many popular coins and includes PIN protection and recovery seed backup.
Trezor Model T
The Trezor Model T is a more advanced device featuring a touchscreen display and additional cryptocurrency support. It provides a smoother user experience while maintaining strong security features.
Both devices support Trezor Login through the official wallet management interface.
How Trezor Login Works
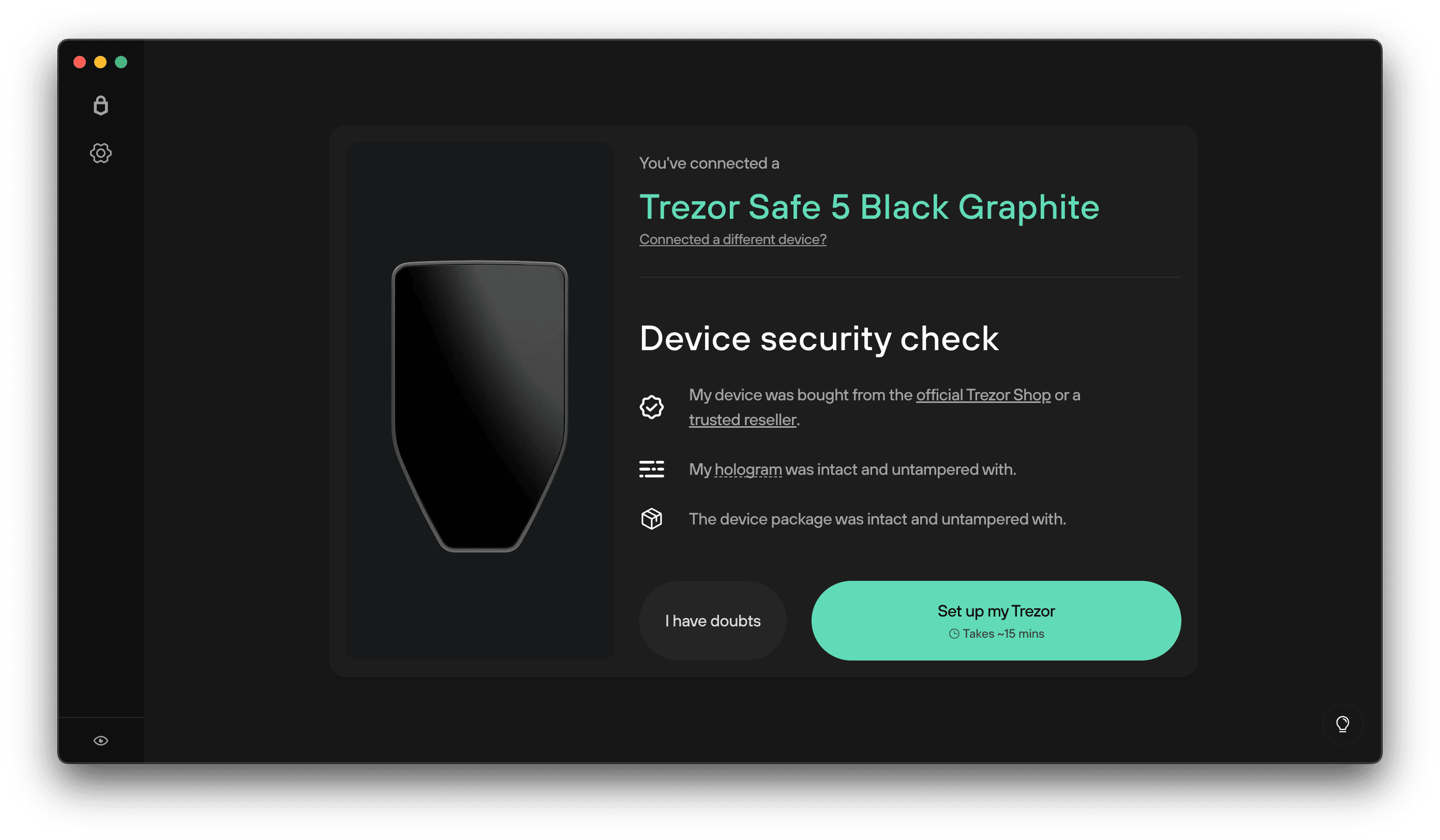
The Trezor Login process uses the hardware wallet as the main authentication tool. When you attempt to access your wallet, the device confirms your identity before allowing access.
Here is how the process works:
- Connect your Trezor hardware wallet to your computer.
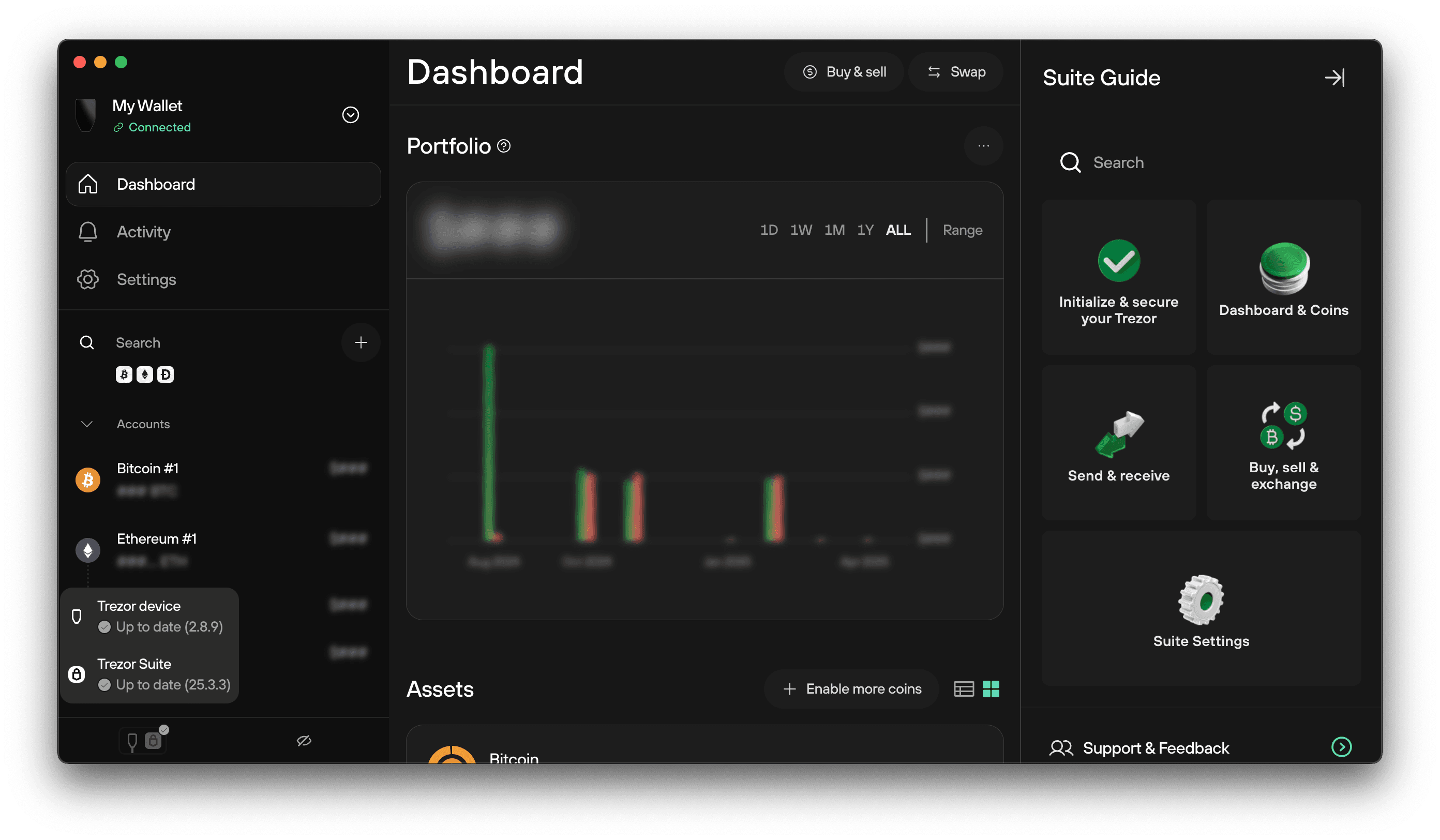
- Open the official Trezor Suite interface.
- Enter your device PIN when prompted.
- The device verifies your identity.
- Once verified, you gain access to your wallet dashboard.
This method ensures that your private keys remain stored securely inside the hardware wallet.
Steps to Access Your Wallet with Trezor Login

Accessing your wallet using Trezor Login is simple and secure. Follow these steps to log in.
Step 1: Open Trezor Suite
Launch the official Trezor Suite desktop application or web interface.
Step 2: Connect Your Trezor Device
Use the USB cable to connect your hardware wallet to your computer.
Step 3: Enter Your PIN
The device will ask you to enter your PIN using the secure interface.
Step 4: Verify on the Device
Your Trezor hardware wallet confirms the login request.
Step 5: Access the Dashboard
After verification, you can view your wallet balance, send or receive cryptocurrency, and manage assets.
Security Features of Trezor Login
Trezor wallets include several advanced security measures that protect user funds.
Offline Private Key Protection
Private keys remain inside the hardware wallet and are never exposed to the internet.
PIN Authentication
Every login requires a PIN entered directly on the device.
Passphrase Security
Users can enable an optional passphrase for additional wallet protection.
Transaction Verification
Every transaction must be confirmed on the hardware wallet screen.
Open-Source Security
Trezor software is open-source, allowing independent security audits.
Benefits of Using Trezor Login
Using Trezor Login provides several advantages compared to traditional online wallets.
- Enhanced protection from hacking attempts
- Secure hardware-based authentication
- Protection against phishing attacks
- Complete control over private keys
- Compatibility with many cryptocurrencies
This system ensures that your cryptocurrency remains protected even if your computer becomes compromised.
Best Practices for Secure Login
To maintain strong security while using Trezor Login, follow these recommendations:
- Always use the official Trezor software
- Never share your recovery seed phrase
- Use a strong PIN code
- Enable passphrase protection if needed
- Keep your device firmware updated
Following these best practices helps keep your digital assets safe.
Managing Cryptocurrency After Login
After completing the Trezor Login process, users can manage their cryptocurrency using Trezor Suite.
Features available include:
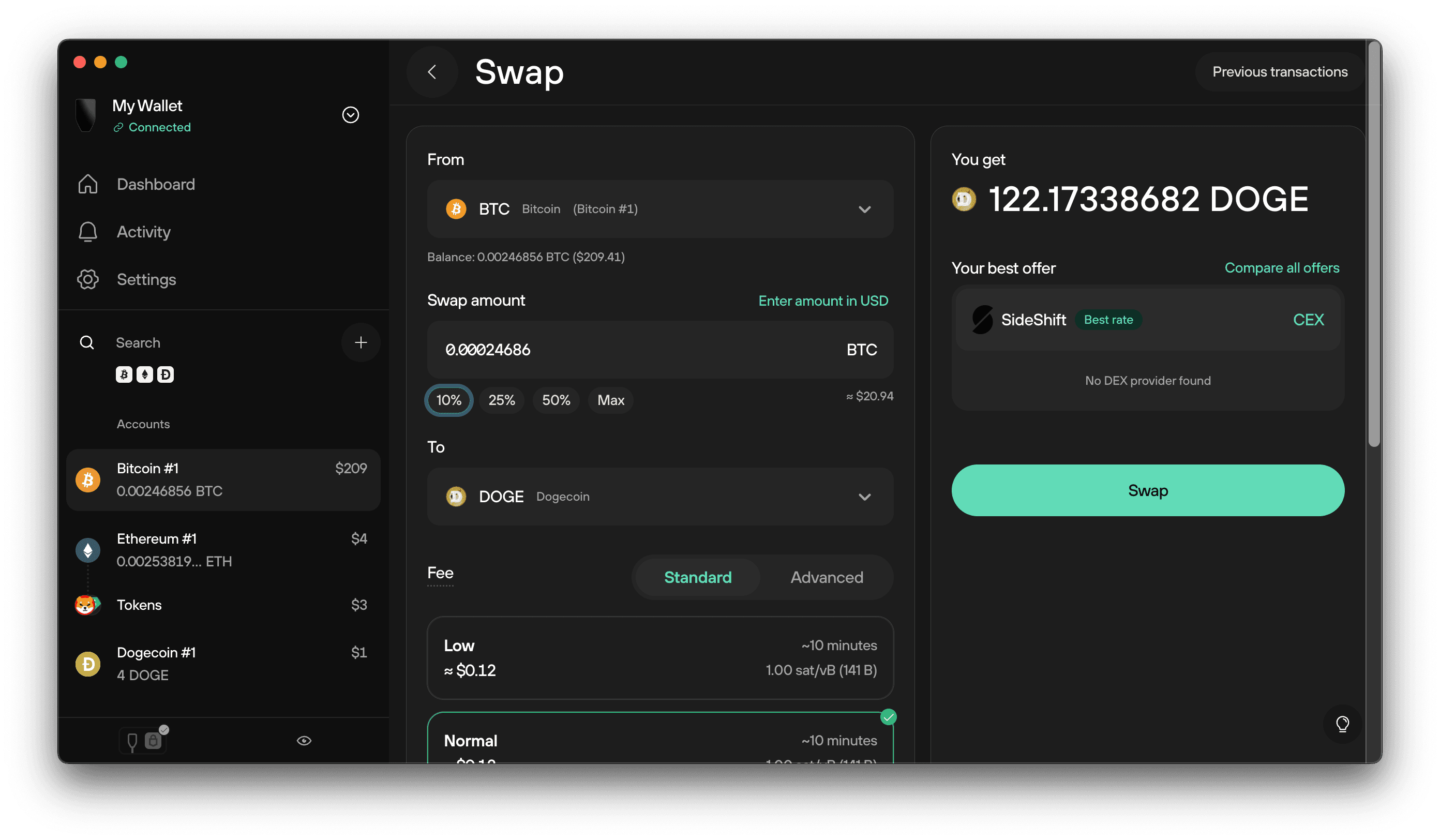
- Sending and receiving digital assets
- Monitoring portfolio balances
- Managing multiple cryptocurrency accounts
- Viewing transaction history
- Accessing additional wallet features
The interface provides a simple and secure environment for managing cryptocurrency holdings.
Frequently Asked Questions (FAQs)
What is Trezor Login?
Trezor Login is the secure process used to access a Trezor hardware wallet through the official wallet interface.
Do I need my Trezor device to log in?
Yes, the hardware wallet is required for authentication and security verification.
What happens if I forget my PIN?
You can reset the device and restore your wallet using the recovery seed phrase.
Can I access my wallet without the device?
No, the Trezor hardware wallet is required to authorize login and transactions.
Is Trezor Login safe?
Yes, it uses hardware-based security that keeps private keys offline and protected from online threats.
Footer
Trezor hardware wallets provide one of the most secure ways to manage cryptocurrency. Using Trezor Login ensures that access to your wallet is protected through hardware authentication and secure verification.
This system helps protect private keys, reduce the risk of phishing attacks, and give users full control over their digital assets.
Disclaimer: This content is for informational purposes only and is not affiliated with or officially endorsed by Trezor or its parent company.